If you read our recent blog on top 10 cybersecurity SEO strategies for 2026, you already know that you need to do much more to win in the SEO landscape for cybersecurity.
Google is no longer the only search engine that matters. ChatGPT, Perplexity, Gemini, and Claude are now actively shaping how your buyers discover, evaluate, and shortlist cybersecurity vendors.
The stats also confirm this shift.
Gartner predicted that traditional search engine volume would drop 25% by 2026, with AI chatbots and virtual agents absorbing that share.
AI referral traffic is growing at roughly 1% month-over-month, and ChatGPT alone drives nearly 88% of that AI-sourced traffic. Meanwhile, AI Overviews now appear in over 25% of Google searches, up from around 13% in early 2025.
For cybersecurity founders, this creates a very specific challenge.
Your buyers, CISOs, compliance officers, IT heads, are increasingly asking AI tools questions like “which MSSP is best for SOC 2 compliance?” or “how do I evaluate a pentest vendor?”.
If your blog content is not structured, credible, and extractable enough for AI engines to cite, you will not be part of that answer.
And being left out of the AI answer is the new version of being stuck on page 5 of Google.
This blog is built for cyber founders who want to understand how AI SEO for cybersecurity works at the blog level, and how to write blogs that not only rank on Google but also get featured, cited, and recommended by AI search engines.
We are going to walk through the entire process. From understanding how AI engines choose what to cite, to structuring your writing for extraction, to measuring whether it is actually working.
Why Traditional Blogs for Cybersecurity No Longer Cut It
Most cybersecurity blogs today are written for one audience: Google’s traditional algorithm. That means keyword targeting, backlink building, and meta descriptions. These still matter, but they are no longer sufficient.
Here is what has changed. AI engines like ChatGPT and Perplexity do not rank pages the way Google does.
They do not look at your page and think, “This has 40 backlinks and a keyword density of 2.3%, so let’s show it.”
Instead, they scan content for clarity, structure, direct answers, and authority signals, and then decide whether to extract from it and cite it.
Research shows that ranking first on Google does not guarantee AI citation. A lower-authority site with precise, well-structured, and highly relevant content can outperform a high-authority site that has vague or outdated information in AI responses.
Brand mentions across the web correlate more strongly with AI visibility than backlinks alone.
For cybersecurity companies, this is both a threat and a massive opportunity. The threat is that your competitors who optimize for AI SEO early will establish compounding visibility advantages.
The opportunity is that AI search visitors convert at significantly higher rates than traditional organic visitors, because they arrive already pre-qualified. They have already read about you in the AI’s response, and they are clicking through with intent.
This is why writing AI SEO blogs for cybersecurity demands a different playbook than what most agencies and in-house teams are running today.
How AI Engines Decide What to Cite from Your Cybersecurity Blog
Before you change how you write, you need to understand how AI engines choose sources. This is where most cybersecurity SEO strategies fall short. They optimize for Google without understanding the AI citation layer.
ChatGPT
ChatGPT relies heavily on Bing’s index and trusted web data. It looks for clear entity signals, meaning it needs to understand who you are, what your brand does, and what domain expertise you represent.
It favors structured summaries, consistent topical depth, and content that directly addresses a question without fluff. When your brand shows up consistently around one topic across multiple pages, ChatGPT starts to connect the dots and recommend you.
Perplexity
Perplexity crawls the web in real time and displays its citations openly. Its architecture is citation-first, meaning it prefers sources with clear, quotable paragraphs. Short, direct answers win.
Formatting plays a bigger role here than on ChatGPT. If your content is easy to extract and clearly structured, Perplexity is far more likely to reference it. Its top citation sources include Reddit, YouTube, and authoritative industry sites.
Google AI Overviews
Google’s AI Overviews have the strongest correlation with traditional search rankings. Over 76% of URLs cited in AI Overviews also rank in the top 10 of Google search results.
But here is the critical nuance: AI Overviews and Google’s AI Mode cite different sources, with only about 14% citation overlap between the two. So optimizing for one does not guarantee visibility on the other.
The Common Thread
Across all AI engines, three factors consistently determine whether your cybersecurity blog gets cited:
1. Structural clarity: Clean headings, short paragraphs, direct answers near the top, FAQ sections, and comparison tables.
2. Authority and trust signals: Author credentials, brand mentions on third-party platforms (Reddit, G2, review sites), schema markup, and original research or data.
3. Content that is easy to extract: Nearly 44% of all AI citations come from the first 30% of an article’s text. Your intro and opening sections carry disproportionate weight.
Step-by-Step Process: Writing AI SEO Blogs for Cybersecurity
Here is the exact process we recommend to cybersecurity founders who want their blogs to perform on both traditional search engines and AI platforms.
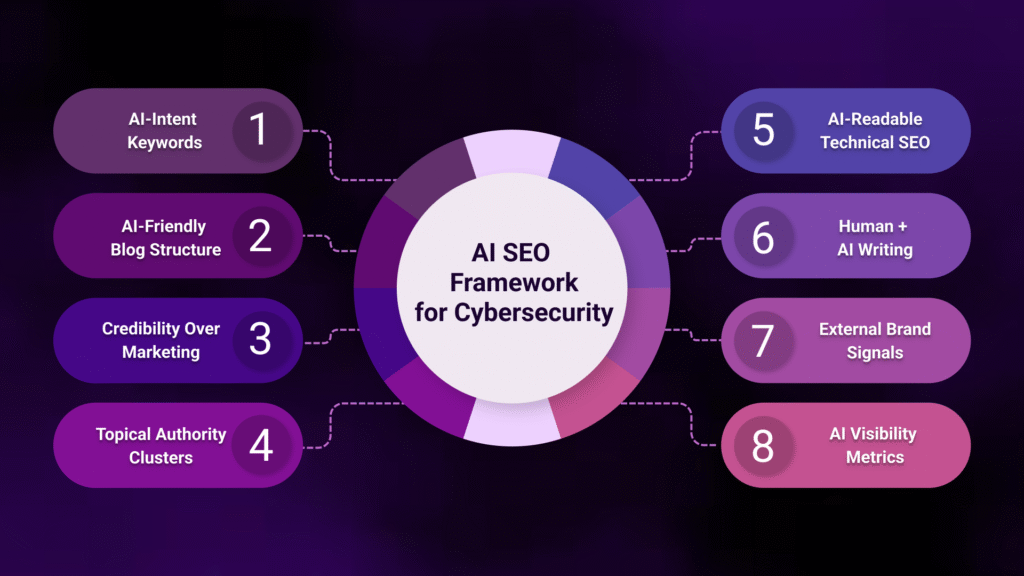
Step 1: Start With AI-Intent Keyword Research, Not Just Google Keywords
Traditional keyword research tools give you search volume and competition data for Google. That is useful, but it is incomplete for AI SEO cybersecurity strategy.
AI search is driven by prompts. People do not type two-word queries into ChatGPT. They ask full, conversational questions. They compare options. They request step-by-step plans. Your content should reflect that.
What to do: Take your target keywords like “penetration testing services” or “how to prepare for SOC 2 compliance” and then think about what your actual buyers, the CISOs, IT heads, and compliance officers, are typing into AI tools about security and compliance.
For example, if you offer penetration testing or GRC services, your buyers might be prompting AI tools with questions like:
“How often should a SaaS startup get a penetration test done for SOC 2?”
“What is the difference between a vulnerability assessment and a penetration test?”
“Which MSSP is best for HIPAA compliance monitoring for mid-size healthcare companies?”
Then, manually test these buyer-side prompts in ChatGPT, Perplexity, and Gemini. Note which cybersecurity vendors are being cited. Note the format and depth of the content being cited. This is your AI competitive landscape.
If a competitor’s blog on SOC 2 pentesting frequency is getting cited and yours is not, that tells you exactly where to focus. Your keyword strategy should start here, with the questions your buyers are already asking AI, and then work backwards into the blog topics and structures that answer them.
Step 2: Structure Every Blog for AI Extraction, Not Just Readability
This is the most critical and most overlooked step in cybersecurity SEO strategies for the AI age. Your blog structure determines whether AI can cleanly extract your points or whether it skips you entirely.
The Direct Answer Rule
Right after your introduction, provide a concise, paragraph-long direct answer to the main question your blog addresses. This is not a summary. It is a standalone answer that an AI engine can extract and present verbatim. Think of it as your blog’s “elevator pitch” to a machine.
Heading Hierarchy
Use H2s and H3s that mirror the exact questions your audience is typing into AI tools. Instead of a creative heading like “The Great SEO Awakening,” use “How to Structure Cybersecurity Blog Content for AI Search Engines.” AI engines parse your heading tags to understand the content structure. Vague or clever headings get ignored.
Short, Self-Contained Paragraphs
Each paragraph should be able to stand alone as a quotable answer. Perplexity in particular favours content where it can pull a 2–3 sentence block that fully answers a sub-question without needing the surrounding context.
Use Comparison Tables and Step Lists
Whenever you compare two approaches, frameworks, or tools, use a table. Whenever you describe a process, use numbered steps. These formats are significantly more likely to be extracted by AI engines than running prose.
Step 3: Lead With Credibility, Not Marketing Language
AI engines think in solutions and less in terms of the superlatives that are often used. A page full of “industry-leading,” “cutting-edge,” and “next-generation” signals marketing copy, not authority. And AI systems are trained to deprioritize content that reads like a sales pitch.
For cybersecurity blogs specifically, this is doubly important because Google considers cybersecurity content as high-stakes information under its E-E-A-T guidelines (Experience, Expertise, Authoritativeness, Trustworthiness).
Wrong information in cybersecurity can cause real harm. So search engines and AI systems are stricter about what they surface.
What to do instead:
Back every claim with data: Do not write “most companies struggle with compliance.” Write “IBM’s 2024 Cost of a Data Breach Report found that the global average breach cost reached USD 4.88 million, making compliance failures increasingly expensive.” Content that includes original statistics or properly attributed data points sees significantly higher visibility in AI responses.
Add author identity: Author name, role, credentials, and organizational background provide critical authority signals to AI engines. If your founder has 15 years in penetration testing, that should be visible on every blog they publish. Implement author schema markup to make this machine-readable.
Cite your sources: For every significant claim in your blog, add a verified statistic or source. This gives AI systems the confidence to extract and attribute your content. It also positions your blog as a trustworthy aggregation point, which increases the likelihood of being cited.
Step 4: Build Topical Authority Through Content Clusters
AI engines do not evaluate a single blog post in isolation. They evaluate your entire domain’s authority around a topic. If you publish one blog about VAPT and then your next blog is about email marketing tips, AI systems have no reason to consider you an authority on security testing.
For AI SEO blogs in cybersecurity, you need topical clusters. This means creating a pillar page on a core topic, say “Penetration Testing Services,” and then building a cluster of 8–12 supporting blogs that cover subtopics: how to scope a pentest, what to expect from a pentest report, how to prioritise findings, pentest frequency for SOC 2 compliance, and so on.
Each blog in the cluster interlinks to the others and to the pillar page. This serves two purposes. First, it signals to Google and AI engines that your site has comprehensive depth on this topic. Second, it creates multiple entry points for AI citation.
If an AI user asks about pentest scoping, your scoping blog gets cited. If they ask about findings prioritisation, that blog gets cited. Either way, your brand is in the conversation.
We covered this in more depth in our top 10 cybersecurity SEO strategies blog, where we discussed how pillar-cluster architecture specifically supports the cybersecurity buyer journey.
Step 5: Implement Technical SEO Signals That AI Engines Read
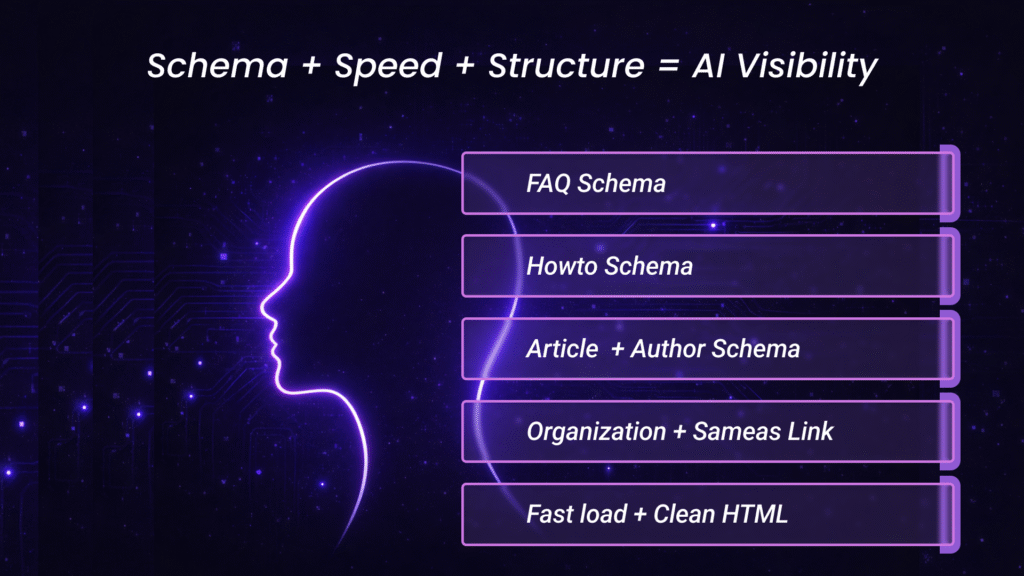
Content quality gets you considered. Technical signals get you cited. Here are the non-negotiables for SEO for cybersecurity blogs that want AI visibility:
FAQ Schema: This is what many experts call “AI gold.” Perplexity and Gemini frequently pull answers directly from correctly marked-up FAQ sections. Every cybersecurity blog should have a structured FAQ section at the bottom with schema markup.
HowTo Schema: For any blog that describes a process (how to prepare for a SOC 2 audit, how to evaluate an MSSP, how to respond to a breach notification), implement HowTo schema. This provides AI engines with a clean, ordered list that is easy to extract and present.
Article and Author Schema: Make sure every blog has proper Article schema with author credentials, publication date, and organisation details. This is how AI engines verify that the content comes from a credible source.
Organisation Schema with SameAs: Link your brand identity across platforms (LinkedIn, G2, Crunchbase, your website) using sameAs properties. This helps AI systems build an entity graph of your brand, which increases the likelihood that they will recommend you by name.
Fast Loading and Clean HTML: AI crawlers, especially Perplexity’s, behave similarly to search engine bots. If your page is slow to load, has broken redirects, or blocks crawlers, it will not get indexed for AI citation. Over 63% of ChatGPT agent visits bounced immediately due to HTTP errors, slow loading, or bot-blocking rules. Make sure your technical foundation is solid.
Step 6: Write for Both the Human Buyer and the AI Extractor
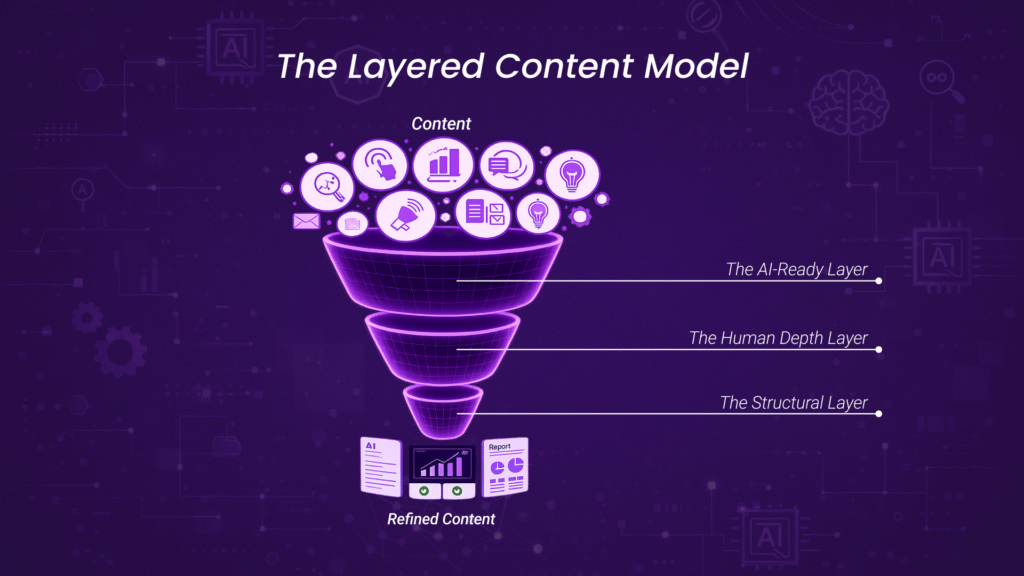
There is a tension in writing blogs for cybersecurity that work for both audiences. Your human reader, a CISO or compliance lead, wants depth, nuance, and business context. The AI extractor wants short, clean, directly quotable blocks.
The solution is not to choose one over the other. It is to layer your content.
Layer 1 – The AI-Ready Layer: Lead every section with a direct, clear answer in 2–3 sentences. This is what AI engines will extract. Make it factual, specific, and standalone.
Layer 2 – The Human Depth Layer: Follow the direct answer with deeper explanation, examples, context, and business implications. This is what keeps your human reader engaged and builds trust. This layer is what converts a visitor into a lead.
Layer 3 – The Structural Layer: Use comparison tables, step-by-step breakdowns, TL;DR summaries, and FAQ sections that serve both audiences simultaneously. These formats are easy for AI to extract and helpful for human readers scanning for quick insights.
This layered approach means your blog does double duty. It gets cited by AI engines (driving pre-qualified traffic), and it converts that traffic when human readers arrive on the page.
Step 7: Build External Brand Signals for AI Citation
Writing a great blog is necessary but not sufficient. AI engines, particularly ChatGPT, look at external validation to decide whether to cite you. This is where most cybersecurity companies underinvest.
Domains with active presence on platforms like G2, Capterra, Trustpilot, and review sites have significantly higher chances of being cited by ChatGPT compared to sites without such presence. Similarly, domains with substantial brand mentions on forums like Reddit and Quora see roughly four times higher citation rates.
Actionable steps:
Get listed and reviewed on platforms your buyers already use: G2, Capterra, Clutch, and relevant cybersecurity directories.
Participate authentically on Reddit in cybersecurity subreddits, answering real questions with genuine expertise.
Publish original research or data that others will cite. If you have a unique dataset, like response times, compliance timelines, or breach patterns from your client work, package it as a blog or report. Original data is content that AI engines must cite because it exists nowhere else.
Ensure your brand Wikipedia page, Crunchbase profile, and LinkedIn company page are complete, current, and consistent with your website messaging.
Step 8: Measure AI Visibility, Not Just Google Rankings
This is where most teams go wrong. They measure the success of their cybersecurity SEO strategies entirely through Google Search Console and traditional ranking tools. In 2026, that is only half the picture.
How to track AI visibility:
Monitor AI referral traffic: In GA4, create a custom report filtering referral sources for chat.openai.com and perplexity.ai. The numbers may be small initially, but they show whether AI systems are actually surfacing your brand.
Manual citation testing: Every month, take your top 30–50 target queries and search them across ChatGPT, Perplexity, Gemini, and Claude. Document whether your brand appears, which competitors are cited, and what type of content earns citations. This becomes your AI visibility scorecard.
Track branded search volume: If your AI visibility is working, you should see an increase in branded search queries over time, because people who encounter your brand in AI responses will then search for you directly.
Add attribution questions: In your lead forms, add “How did you hear about us?” with options that include ChatGPT, Perplexity, AI search tool, and Google AI Overview. You need data on how much AI-driven discovery you are getting or missing.
A Quick Checklist Before You Publish Your Next Cybersecurity Blog
Before hitting publish on any blog, run through this checklist:
Does the blog have a clear, direct answer to the main question within the first two paragraphs?
Are your H2s and H3s written as specific questions or clear topic labels, not vague or creative headlines?
Can each major paragraph stand alone as a quotable block if an AI engine extracts it?
Have you backed up every significant claim with data, a source, or a clear attribution?
Is there a structured FAQ section at the bottom with FAQ schema markup?
Does the author bio include real credentials, role, and expertise relevant to the topic?
Is the blog part of a topical cluster, with internal links to related pillar and supporting content?
Are Article, Author, and Organisation schemas properly implemented?
Is the page fast-loading, mobile-responsive, and not blocking AI crawlers?
Have you tested the blog’s core topic as a query in ChatGPT and Perplexity to see what currently gets cited?
The Bottom Line for Cyber Founders
AI SEO cybersecurity is not a separate discipline from regular SEO. It is the evolution of SEO, and it demands that your content be clearer, more credible, better structured, and more externally validated than what came before.
The cybersecurity companies that invest in writing AI SEO worthy blogs for cybersecurity now are building an advantage that compounds over time, exactly like the companies that invested in traditional SEO early captured disproportionate organic traffic for years.
If you have read this far and are thinking about how to apply this to your own content, start with one blog. Pick your most important topic.
Restructure it using the steps above. Test it in AI tools. Measure the difference. Then scale.
And if you want help executing this, that is exactly what we do at Digi-Tx. We work with cybersecurity companies to build content strategies that perform on both Google and AI search, because in 2026, you need both.




